DevSecOps – A Trusty Sidekick to Your DevOps-Superhero

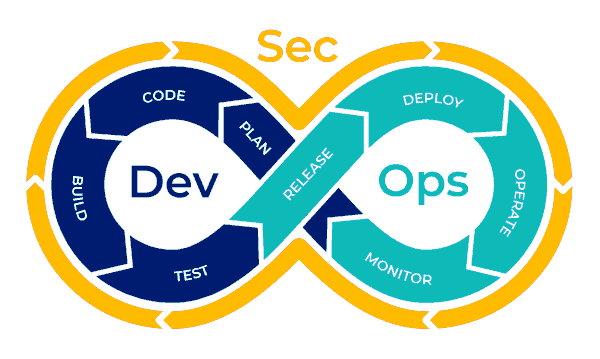
What is DevSecOps?
Security can no longer be “a phase” at the end of development pipelines, rather needs to be built into every stage of the continuous delivery pipeline.
The changing landscape of Application Development, Data Protection, Infrastructure Optimization, and Security Compliance Standards across the world has altered the outlook of security in a business environment. DevSecOps “integrates security at every stage of the Software Delivery Pipeline to eliminate any threats, risks, attacks, and downtime in the process”.
In recent years, companies that have used DevOps to combine development and operations teams and have been largely successful in releasing products at a significantly faster rate. However, the sooner you release code, the risk of vulnerabilities sneaking out in the process is higher as well. This has lead to the rising need for security to be included throughout the development process.
The Rise of DevSecOps
74% of IT leaders confirmed an increase in accelerating initiatives to improve security across their software development lifecycle.
The year 2020 has been a testing period for businesses world over. The pandemic dramatically accelerated the pace of digital transformation across industries. Most organizations, who were not on it already, were compelled to move to the cloud and use digital tools to continue BAU virtually. However, that led to a mounting concern over data security. After all, with everybody working remotely, and chances of data breaches were substantially higher. Research showed a whopping 273% increase in data breaches in the first half of 2020 as compared to 2019.
Soon, many leaders in organizations which were already practicing the DevOps model realized the value DevSecOps could bring to the table.
Key Aspects of DevSecOps Implementation
Vulnerability Scanning and Security Training
Incorporating vulnerability scanning into your DevOps process is the best place to begin your DevSecOps journey. This means that the code is checked for any possible vulnerabilities at every stage of its delivery process. The most important factor that must be considered for integrating this practice is to make sure that the stakeholders involved at each stage of the cycle have complete guidance and knowledge of handling the tools to detect the vulnerabilities in code.

Run-time Protection
Run time protection helps secure software against any possible runtime threats that can arise when the application starts running. While people consider runtime threats are only centered around production, they can exist at any point of the DevOps cycle, and mitigating them is an crucial part of implementing a successful DevSecOps strategy.

Leveraging Cloud Services to Implement DevSecOps
All cloud service providers in the market have considered security as their top priority for any service offering. Right from securely integrating with source code repositories to supporting the application for monitoring throughout its lifecycle, cloud providers use different DevSecOps strategies to deliver security as a service for clients.
Some of them include restricting access control using Identity management, enabling multi-factor authentication at source code access level, scanning the container images using security scanners, applying policies to CI/CD pipelines for post-deployment gateways, enabling key vaults in the pipeline to store all passwords and sensitive information and enforcing active threat monitoring and performance analytics after deployment.
While different cloud providers have different services enabling all the above-mentioned security guidelines, the ultimate goal of all these providers is to enforce a successful DevSecOps strategy.

Security of Microservices Architectures
The current trend of development shifting from monolithic to microservices architectures have raised the need to validate each piece of environment for any vulnerabilities and unrecognized threats.
While containerization technologies are providing a platform to implement successful microservices-driven architectures, they come with their security challenges like secure communication and isolation of containers, authentication of container registry images, and a need for unified security policies. Aligning with DevSecOps principles is helping developers achieve speed and efficiency in solving the security challenges in such a context.
Tools such as Kubernetes Role-Based Access Control, Service Meshes which can manage the users, applications, and external services, and rapid security testing against various aspects of application security along with using efficient tools for code scanning and reviews have been some key principles in implementing the secure micro services-driven architecture.
Compliance Standards and Policies
The compliance standards enforced by different industries that a solution has to adhere to have raised the standards of security policies across organizations. Administrative norms like PCI DSS, HIPAA, and ISO 27001 endorse proposals for ensuring information and improving data security.

Adopting DevSecOps as a Practice
DevSecOps is a way of approaching software development with a mindset of “everyone is responsible for security”.
It would require you to make automation your friend. Implementing DevSecOps may not be limited to using some security tools and restricting to depend on a set of practices, it is a holistic approach in which all the stakeholders, from developers, testers to security teams embrace it as a culture and take responsibility to integrate stronger security at every phase of software development and delivery.
Read the next blogs in this series to learn more about DevSecOps. Talk to our experts to explore the value implementation of DevSecOps would have on your software development outcomes.
“
Security is a process. Not a product.
Bruce Schneier




